Using Generative AI to create deceptions for Identity Protection
Generative AI has taken the world by storm. It has become an exciting and rapidly developing field that involves the creation of images, videos, music, text, and other data using generative AI models. According to a Gartner article, AI-powered chatbots are just the beginning; enterprise uses for generative AI are far more sophisticated. The Gartner article summarizes several applications of generative AI in healthcare, marketing, and other industries. Here, we discuss how Generative AI can be leveraged for cybersecurity, specifically for identity protection.
Most data breaches involve attacks on identities. The SolarWinds/APT 29 attack, Twitter breach, and ransomware attacks by LockBit and REvil are examples of high-profile attacks that involved identity compromises.
Attackers can launch identity attacks by using openly available tools such as Mimikatz and LaZagne to access cached credentials on endpoints. Attackers might also use brute force techniques like password spraying and credential stuffing to attack identity artifacts such as NTLM hashes, Kerberos tickets, and SAML tokens. They can exploit user/service account misconfigurations that provide credential access through identity-specific offensive techniques, such as Kerberoasting and AS-REP Roasting. They are attacking identity stores such as Active Directory (AD), AzureAD, Azure AD Connect, Active Directory Federation Services (ADFS), and Active Directory Certification Services (ADCS). By using DCSync/DCShadow attacks against AD, attackers can gain access to the credentials of any account and disable MFA policies.
Identity threats are a serious problem, and enterprises need to prioritize and make identity defense an integral part of the overall cybersecurity strategy.
Acalvio’s Active Directory Protection solution discovers identities from various enterprise identity stores such as AD, ADCS, AzureAD & M365, and identifies attack surfaces that an attacker can exploit. The solution also identifies key assets that are at high risk of being attacked. Typically, attackers target key assets and privileged user/service accounts associated with them. For example, network shares may have cached credentials of domain admins/privileged accounts. An attacker would attempt lateral movement to a network share to gain access to these credentials. Similarly, an enterprise may have several Kerberoastable service accounts and their credentials may be cached on various endpoints. The Acalvio solution discovers all such attack surface elements that can be exploited by an attacker.
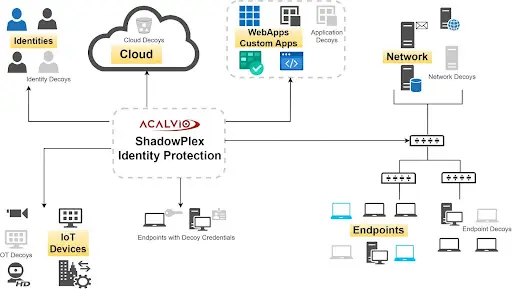
In recent years, the use of Generative AI has shown great potential for enhancing cybersecurity. The Acalvio solution employs Generative AI to recommend decoy identities to be added to AD and decoy tokens to be placed on real endpoints. The deception types and their placements are determined by AI algorithms so that the deceptions can lure, deceive, and divert advanced threats lurking inside the enterprise network. These AI algorithms can recommend thousands of decoy identities and decoy tokens that can be added to identity stores like AD and endpoints, respectively. As shown in the above figure, by combining systems engineering with Generative AI, the Acalvio solution creates deceptions for all types of assets, such as decoy identities for Active Directory, decoy tokens for endpoints, decoy computers for networks, decoy IOT devices, and so on. The Al algorithm computes the number of deceptions (or deception density), deception types, and deception placements, and also makes the deceptions attractive so that attackers interact with them. By combining Generative AI with other AI algorithms, the Acalvio solution can ensure that the deceptions blend well with enterprise identities and network assets.
Deceptions deployed by the Acalvio solution raise alerts when an attacker interacts with them. These alerts are high-fidelity alerts because enterprise users would not interact with the deceptions.
AI algorithms in Acalvio’s solution can also identify thousands of attack paths to key assets and the attack surface that an attacker can exploit to take over key assets. These attack paths are identified by combining data from multiple data sources (AD, Azure AD, endpoints, applications). Information about these attack paths is leveraged to determine the best placement locations for deceptions.
The Acalvio approach is free of false positive challenges associated with traditional, anomaly-based detection mechanisms. Also, deception-based identity threat defense does not leverage signatures or rules and so it does not need to be updated for new identity threats. Acalvio’s Identity Theft and Detection Response provides a solution to protect identities using a novel set of AI algorithms, Generative AI, and systems engineering.

