CSA’s Mythos Advisory Asks CISOs to Set a 90-Day Clock for Deception Programs. Learn Why.
CSA and security experts’ expedited strategy briefing on Mythos
The urgency of the advances highlighted in the Mythos publications has triggered a series of emergency responses. The Cloud Security Alliance (CSA) CISO Community, in collaboration with SANS, [un]prompted, OWASP Gen AI Security Project, and the wider security community, published an expedited strategy briefing on Mythos, designed for CISOs. This advisory outlines a series of steps for security teams to prepare their programs for advances in foundation models. The advisory is available at: https://labs.cloudsecurityalliance.org/mythos-ciso/.
The advisory calls for deception as a necessary control to combat advances in vulnerability exploitation stemming from attacker actions involving Mythos (or equivalent) models. The advisory recommends that CISOs set a 90-day clock for building deception capabilities.
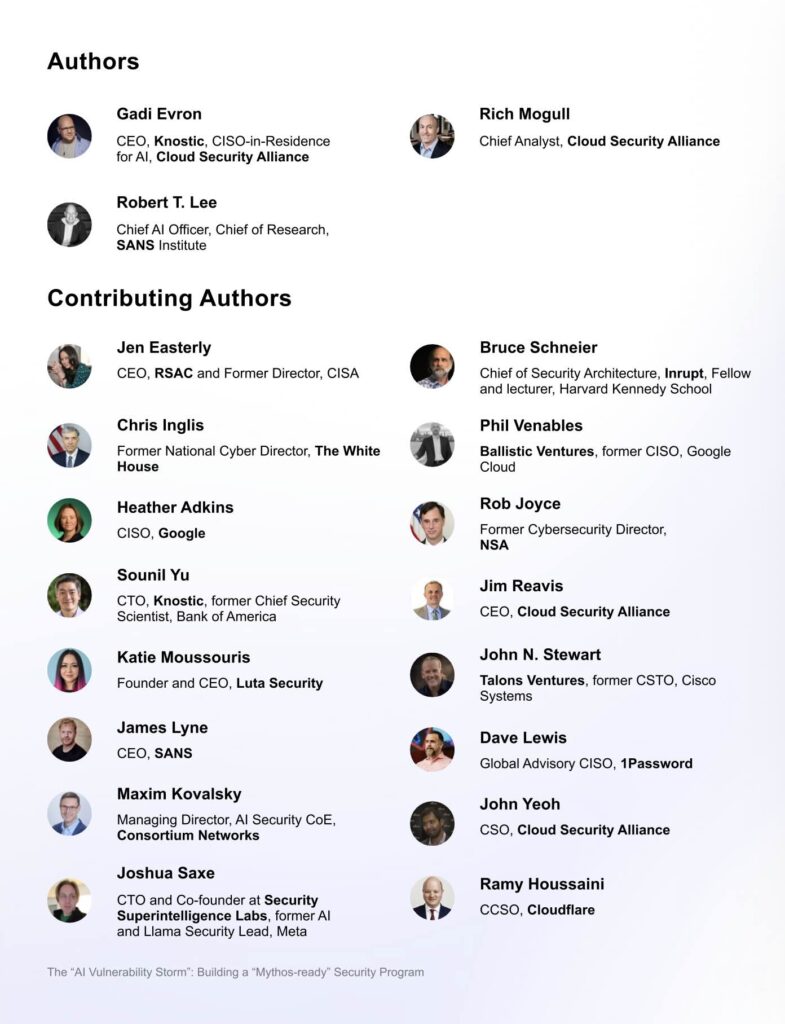
The authors of this briefing are Gadi Evron, CEO, Knostic, CISO-in-Residence for AI, Cloud Security Alliance; Rich Mogull, Chief Analyst, Cloud Security Alliance; and Rob T. Lee, Chief AI Officer, Chief of Research, SANS Institute.
Contributing authors include, Jen Easterly (CEO, RSA Conference, former Director of CISA), Bruce Schneier (Fellow and lecturer, Harvard Kennedy School), Chris Inglis (former National Cyber Director, The White House), Rob Joyce (former Cybersecurity Director, NSA), Heather Adkins (CISO, Google), Joshua Saxe (CTO and Co-founder at Security Superintelligence Labs), Sounil Yu (CTO, Knostic, former Chief Security Scientist, Bank of America), John N. Stewart (former CSTO, Cisco Systems), and Phil Venables (former CISO of Google Cloud).
More than 250 CISOs edited and redlined this briefing.
What is Anthropic Claude Mythos?
Anthropic Claude Mythos is the new (unreleased) general-purpose model from Anthropic. The model has been trained on a large corpus of source code, documentation, and programming languages. A large set of open-source code has been included in the training data. The model has advanced reasoning capabilities that represent significant advances in multi-step planning and logic.
Anthropic has published an analysis that highlights the model provides strikingly effective results for cybersecurity use cases, especially around finding vulnerabilities. Mythos has found thousands of vulnerabilities in major operating systems and browsers, including chained exploits in the Linux kernel and remote code execution (RCE) in one of the most hardened operating systems (OpenBSD).
What is the cyber risk associated with Mythos?
Claude Mythos is currently not released in the public domain. However, these advances have sparked concern in the industry about the ramifications of advanced LLM-based reasoning capabilities when they fall into the hands of attackers.
Volume of vulnerabilities
Mythos has surfaced advances in Frontier AI models in finding and exploiting vulnerabilities at a rate that significantly exceeds previous-generation AI models. Defenders will use Mythos equivalent models to find vulnerabilities ahead of the attacker. Even though this has strong defensive implications and improvements, the attacker continues to have an advantage, as the attacker can leverage Frontier AI models that the defender does not have access to.
Zero days
One of the key advances in Claude Mythos is the ability to find unknown exploits (or zero days). The model’s advanced reasoning capabilities highlight its ability to find novel exploits in both open- and closed-source software.
By definition, a zero-day exploit does not have an associated patch available when it is discovered. As a result, patching the system is not a practical option when the defender faces attacks that exploit zero-day vulnerabilities. There would be no patch available to apply.
The risk of zero days and the challenges of patch application are not new. What is new with Mythos is the ease with which these exploits can be made practical for the attacker. An attacker equipped with Mythos (or an equivalent) model can now find a large number of zero-days and exploit them in parallel.
What was earlier possible but required nation-state-equivalent skills from the adversary is now possible with an adversary far less skilled. A relatively simple prompt is sufficient to execute these exploits.
This is the cyber risk associated with Mythos. An unprecedented event in the cyber landscape.
Are EDR and reactive security controls sufficient to combat Mythos-equipped attacks?
Let us analyze both aspects of the security risk posed by Mythos.
Volume of vulnerabilities: as the exploitable set of vulnerabilities grows, defenders will find it increasingly difficult to keep the patch application levels consistent with the threat. Patching applications has always been difficult; the backlog grows far more rapidly with the increase in the volume of patches that need to be applied.
As patches lag, an attacker outside the organization can leverage a Mythos-equivalent Frontier AI model to exploit associated vulnerabilities in internet-facing assets and gain initial access. Once the attacker gains access, the propagation inside the network occurs at machine speed.
Zero days: Consider an attack path: the Mythos-equipped attacker finds and exploits a novel vulnerability in an internet-facing asset and gains remote code execution. The attacker finds a zero-day in a switch and a hypervisor. The attacker encrypts the hypervisor.
This attack bypasses prevention controls because it is a zero-day and no patch is available. The switch and hypervisor are incompatible with agent-based security solutions, such as EDR. The attack also bypasses detection controls. The breach is complete.
This attack path is not new; it has been flagged in several security reports.
The high skill level to perform this exploit would have made this attack path look like a corner case. With Mythos surfacing zero days, the risk associated with this attack path increases by an order of magnitude.
EDR and reactive security controls are designed to combat the human adversary. These controls are based on the principles of observing incoming activity, forming a baseline to identify normal usage, flagging deviations from the baseline, and looking for known patterns in incoming activity. This activity takes time, often taking hours or days. Mythos-equipped exploits occur within minutes and vary with each exploit execution cycle. Reactive controls are slow, the alerts are non-confirmatory, resulting in confusing signals for security teams, and a loss of confirmatory signals for response.
Why has the CSA security advisory flagged deception as a necessary security control?
The security advisory highlights deception as a security control that is independent of specific vulnerabilities or attack TTPs. As attackers leverage Mythos-equivalent AI models to find and exploit zero-day vulnerabilities with no associated patch, defenders need security controls that can detect and deflect attacks, regardless of the specific exploit techniques involved.
Deception has a unique position in a security stack in its ability to detect and deflect these threats without depending on a priori knowledge of the exploit.
By deploying decoys that form a shield around the real assets, defenders gain early warning of incoming exploits and, more importantly, deflect them away from the actual assets.
What assets are at risk for organizations?
Vulnerability exploits can be performed against assets across workload types, including IT and Cloud environments. Since the Mythos equivalent models can find vulnerabilities across a wide variety of operating systems, browsers, and applications, they are applicable to a broad spectrum of assets.
Considerations for prioritizing the rollout of deceptions
In theory, defenders can deploy deceptions across asset types to combat Mythos-equipped attackers. However, practical considerations require a set of criteria for defenders to gain the maximum benefit from a deception rollout, given the time-sensitive nature of the exploit risk.
Defenders can prioritize the mission-critical assets that pose the greatest risk to business impact. Another consideration is prioritizing an approach for legacy or unpatched assets.
By prioritizing key assets (identity architecture, mission-critical business applications, production databases, operational technology assets) and legacy assets (unpatched workstations and servers), defenders can optimize their defensive coverage against a Mythos-equipped adversary.
Acalvio’s platform equips customers to combat Mythos-enabled adversaries through a tailored deception palette that combines decoys representing high-value assets, legacy assets, and honeytokens that identify and mislead the exploits.
To learn more and watch this in action, please schedule a demo.

