What is the WannaCry ransomware attack?
In May 2017, the WannaCry ransomware attack made front-page news around the world, with at least 150 countries and over 200,000 customers affected by the attack. The WannaCry ransomware made use of an exploit that targeted the SMB protocol of Microsoft Windows.
The ransomware attack was able to propagate quickly in the space of a few hours. The rapid spread of this ransomware attack and the dramatic way in which the attack was finally stopped have made this attack an important case study for Security teams around the world.
This blog details the lateral movement techniques used in the WannaCry ransomware attack, the impact of the attack, and other aspects of the attack. For details about other types of lateral movement techniques that have been employed by malware, refer to the published paper in Virus Bulletin.
How did the WannaCry ransomware attack start?
WannaCry is ransomware based on an exploit targeting the SMB protocol of Microsoft Windows. The exploit was developed by the National Security Agency (NSA) of the United States to compromise Windows Servers and Windows desktops (running operating systems of that time, such as Windows XP). A threat actor called the Shadow Brokers stole this exploit from the NSA about a month before the ransomware attack was carried out.
Although Microsoft had released a patch for this exploit, the ransomware group that created the WannaCry ransomware was able to attack a multitude of computers on which the patch had not been applied. This lapse gave the WannaCry ransomware a firm foothold from where it expanded across the globe. The vulnerability in the SMB protocol was used by the ransomware to attack a computer and then pivot to other computers.
A successful attack on a vulnerable machine would result in data files on the computer getting encrypted. The ransomware group had asked for bitcoin in return for decryption keys that could be used to release the encrypted files from the ransomware’s hold.
How did the WannaCry ransomware propagate? What was the lateral movement technique used by the ransomware?
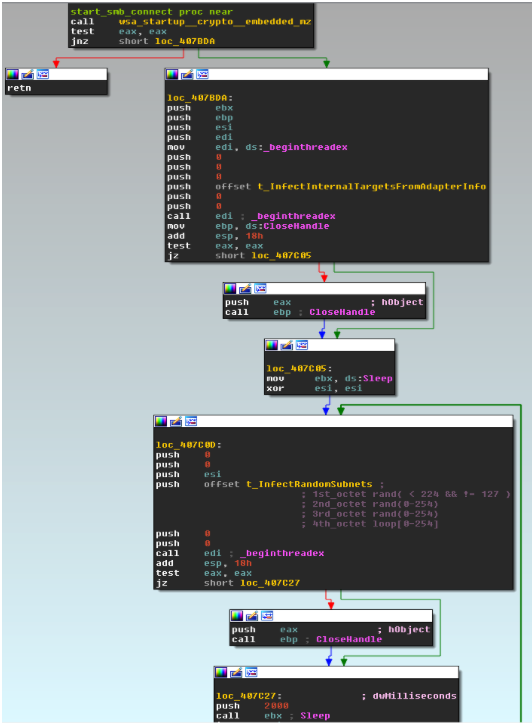
WannaCry ransomware analysis showed that the attack used the Microsoft Windows Server Message Block protocol (SMB) to spread within a network. On a vulnerable machine, the malware’s propagation functionality over SMB is in the “mssecsvc2.0” ServiceHandler function. This function spawns two threads specifically for SMB exploitation: one to infect internal targets and another to infect external targets.
In the internal target infection function, the infected host’s network adapters are enumerated.
In addition, the local DNS servers and gateways are all enumerated by the malware before the malware attempts to spread to them.
The malware checks the IP addresses of local DNS servers to eliminate the possibility that they are public servers. Only the following DNS server ranges are attempted:
10.0.0.0 – 10.255.255.255
172.16.0.0 – 172.31.255.255
192.168.0.0 – 192.168.255.255
In the external spreading function, random IP subnets are enumerated and infection is attempted by the malware. The SMB spreading function is used in both the internal and external spreading functions. It performs an SMB negotiation and then checks for the presence of an implant that indicates whether the target has already been compromised.
If the malware determines that the target is not already infected, it proceeds with the SMBv1 exploit by sending massive Trans2 Requests. After the exploitation attempt, the malware again performs an SMB negotiation and requests another trans response to check whether exploitation succeeded.
If exploitation is successful, then the malware uses the exploited host to propagate itself via the implant.
How was the WannaCry attack stopped in 2017?
A few hours after the WannaCry attack started, an independent security researcher who was studying malware samples from an infected system came upon the kill switch designed by the creators of the malware. From WannaCry ransomware analysis, this researcher saw that the malware would start encrypting data on a computer only if the malware did not receive a response from a specific domain. A quick look at the domain showed that it was not registered. When the researcher registered the domain, the malware on infected computers got a response from the domain, so it did not encrypt data from that point onward.
This discovery of the malware’s kill switch gave other researchers time to collaborate on threat intelligence and come up with decryption keys for files encrypted by the ransomware. These events paved the way for a slow but steady recovery from the ransomware attack.
Does WannaCry still exist?
The SMBv1 vulnerability that enabled the first WannaCry attack has almost been eradicated from networks around the world. But the group that started the attack has not been brought to justice. Security researchers who investigated the first WannaCry ransomware attack found evidence that links the WannaCry ransomware campaign with the Lazarus Group. This is a group of hackers who reportedly enjoy the patronage of the Government of North Korea.
A few other high-profile attacks, such as the Sony Corporation hack, have been attributed to the same threat actor. A ransomware variant of the original WannaCry was used in another attack in August 2018.
What was the impact of the WannaCry attack?
WannaCry ransomware analysis showed that the attack affected more than 200,000 computers across 150 countries. Some estimates of the financial impact of the attack put the damage at close to a few billion US dollars. The attack was stopped just a few hours after it started, by the accidental discovery of a “kill switch” by a security researcher. If the attack had more time to propagate, then the global damage would have been significantly higher.
Healthcare services in the United Kingdom suffered a serious setback due to the attack. Computer systems in many hospitals were rendered inoperable for a while.
Other industries in various parts of the world were affected:
- Telecom companies in Portugal, Saudi Arabia, and Spain
- Petroleum companies in Brazil and China
- Police departments in India and China
- Universities in China and Greece
- Electronics companies in Taiwan and Japan
- State governments in India
- MNCs in the logistics industry
Some ransomware victims might not have come forward to report the attack. So, there is a chance that the actual damage caused by the WannaCry ransomware attack is a lot higher than what has been reported.
What are the steps to detect WannaCry ransomware?
ShadowPlex provides purpose-built deceptions for detecting ransomware attacks like WannaCry—at any stage of the ransomware kill chain. An organization can automatically deploy these deceptions at scale, to protect all segments of the organization’s network: on-premises, cloud, and OT. Automated response actions can be preconfigured in ShadowPlex to respond to the detection of ransomware attacks and directly stop such an attack in its tracks.
What can Security teams do to prevent WannaCry?
Ransomware like WannaCry is designed to leverage a specific set of weaknesses in a network. The primary method to prevent ransomware from spreading is to follow security best practices that are aimed at protecting the network. For example, keeping all systems up to date with patches can go a long way in preventing or at least minimizing the effects of a ransomware infection.
Computer security agencies, such as the United States CISA, recommend implementing an Active Defense system to protect a network against advanced threats like ransomware. A Deception Technology solution like Acalvio ShadowPlex is at the core of an Active Defense system for securing a network.
Conclusion
The severity and impact of the WannaCry ransomware was multiplied by its lateral movement technique. In this blog, we learned about the lateral movement technique employed by the ransomware, which resulted in broad infection in organizations with unpatched Windows computers and limited internal segmentation.
Acalvio ShadowPlex brings the power of deception technology to detect the WannaCry ransomware and isolate any infected endpoint. Detection is extremely fast (under 8 milliseconds), which is crucial to stopping ransomware from encrypting data and spreading to other endpoints.
For additional perspective, our Deception-centric Defense Against Ransomware blog details the advantages of a deception-centric architecture over traditional solutions. Read about why this approach should be part of your security solution strategy, especially if you’re concerned about ransomware.
Frequently Asked Questions
Did WannaCry make money?
The ransom note dropped by the WannaCry ransomware on infected computers asked for payment of USD 300 within 3 days, or USD 600 within 7 days. It is estimated that before the ransomware was reined in, victims paid a total sum of a little over USD 130,000. At the same time, the overall cost of damage caused by the ransomware was projected at USD 4 billion.
What damage did the WannaCry ransomware do?
The WannaCry ransomware attack affected more than 200,000 computers across 150 countries. Enterprises from a diverse range of verticals around the world were impacted by the attack. Many of these enterprises had to stop production for a few days before they could bring all their systems back online.
Some estimates of the financial impact of the attack put the damage at around USD 4 billion. If the “kill switch” for the ransomware had not been discovered, then the damage caused by the attack would have been higher by an order of magnitude.
How was the WannaCry ransomware stopped?
The discovery of a “kill switch” by a security researcher was the main factor in stopping new infections by the ransomware. Other researchers reported that they were able to recover the keys that were used by the ransomware to encrypt files. Together, these breakthroughs helped to stop the attack about 4 days after it started.
How much did WannaCry cost to damage?
It is estimated that victims of the WannaCry ransomware attack paid a total sum of a little over USD 130,000 as ransom for the decryption key from the attackers. The worldwide cost of damage caused by the attack was projected at USD 4 billion.
Who is behind WannaCry ransomware?
Various cybersecurity companies, software development companies, and cybersecurity government agencies have confirmed that the Lazarus Group was behind the WannaCry ransomware attack. This attribution is based on WannaCry ransomware analysis of the code artifacts, ransom note, and tradecraft observed in the attack. The Lazarus Group is reportedly managed by the Government of North Korea.
How did WannaCry spread?
WannaCry leveraged EternalBlue, an exploit built on the SMB protocol by the United States NSA. This exploit was reportedly stolen by a group called the Shadow Brokers, from whom it reached the WannaCry ransomware group. Microsoft had released a patch for the SMB vulnerability, but many enterprises had not applied the patch on their systems.
Why was WannaCry so successful?
Although Microsoft had released a patch for the SMB vulnerability, many enterprises had not installed the patch or had installed the patch on only some systems in their network. This was the main factor that allowed WannaCry to quickly propagate from one computer to the other, across the globe.
Is WannaCry the biggest ransomware attack?
Many cybersecurity researchers and agencies consider the WannaCry attack to be the biggest ransomware attack in terms of the number of systems that were affected.
How to protect from WannaCry?
WannaCry was built around a vulnerability in the SMB protocol. The best way to prevent or at least minimize the impact of ransomware like WannaCry is to keep all systems up to date with patches. Employees can also be trained on following security best practices, such as ways to recognize email-based phishing attacks.
Computer security agencies, such as the United States CISA, recommend implementing an Active Defense system to protect a network against advanced threats like ransomware. A Deception Technology solution like Acalvio ShadowPlex is at the core of an Active Defense system for securing a network.