Lateral Movement Technique Employed by Hidden Cobra
US-Cert recently issued notification regarding malicious cyber activity by the North Korean government [1] Hidden Cobra. There are two families of malware used by the North Korean Government.
- Remote Access Tool (RAT) known as Jonap
- A Server Message Block (SMB) worm called as Brambul worm.
As per the US-Certreport, Hdden Cobra has been using this malware since 2009 to target multiple victims globally and in the United States, including media, aerospace, financial industries, and critical infrastructure sectors.
In this blog, we share the technical details and spreading techniques used by the Brambul worm. Thereafter, we discuss how it can be detected by distributed deception platform.
Brambul Worm
The worm invokes multiple threads which then randomly generates IP addresses for infection.
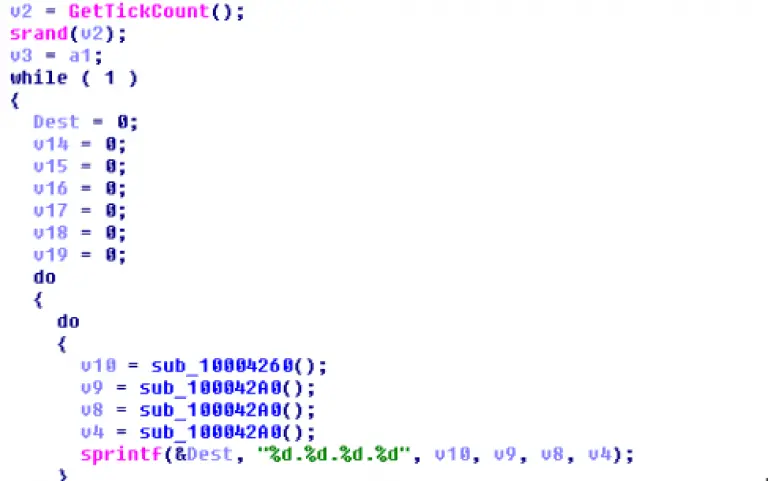
Figure 1.0 Showing the code for random generation of IP address.
Once the victim’s IP addresses have been generated it connects to \\IPC$ share, on the port 445 of the victim machine using Administrator as the username and fixed hardcoded passwords.
Thereafter, the malware code makes a call to the WNetAddConnection2 API to connect to a network resource and constructs the below command.
“cmd.exe /q /c net share admin$=%%SystemRoot%% /GRANT:%s, FULL”
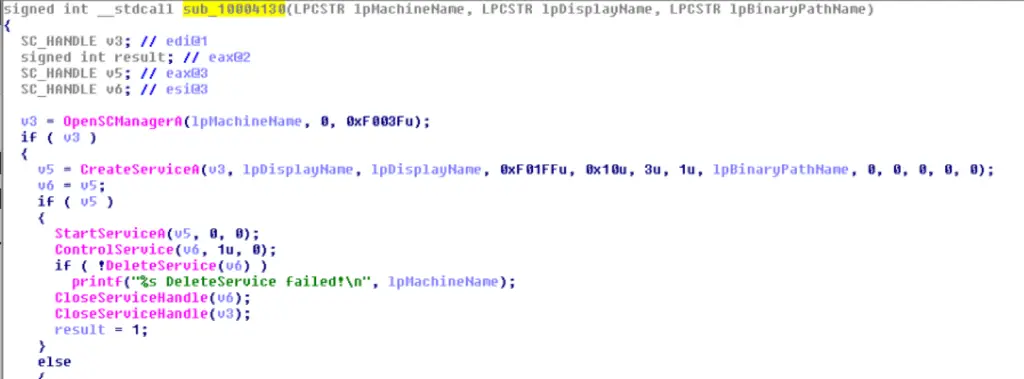
It then makes calls to the service manager. OpenSCManagerA() with the victim machine machines on the network as the parameter. StartSeviceA() then executes the command which grants full permission on the remote machine. Once the command has been executed, the code makes a call to DeleteService() which then deletes the service.
Once the full permission is granted on the remote machine, the worm is copied to the remote machine.
Detection by Distributed Deception Platform
As such, the worm is not quite sophisticated and primarily relies on brute force attempts. This will be successful only in weak environments. If a Distributed Deception Platform is deployed in a threat agnostic manner network, enumeration by the Brambul Worm will get detected with very high confidence. [deployment of a distributed deception platform is discussed in a previous blog]. Brute force attacks on the Distributed Deception Platform leads to isolation of the end-point, thereby containing damage in a timely manner.
References:
[1] Hidden Cobra – North Korean Malicious Cyber Activity.
[2] HIDDEN COBRA – Jonap Backdoor Trojan and Brambul SMB worm

