Ransomware continues to represent the most critical threat facing organizations in 2018. In the latest breaches at Hancock Memorial Hospital, Adams Memorial Hospital, and Allscripts, SamSam ransomware was used to encrypt the files. In this blog, we dive into the technical details of the SamSam ransomware [1]. The blog then shares how the Samsam ransomware can be detected using a deception-based architecture.
Technical Details:
For the Samsam ransomware to execute, it will require input text file as the command line argument. The input text file will have the base64 encoded public keys in the XML format shown in figure 1.0
When the ransomware code is executed, it drops two files selfdel.exe and del.exe. Selfdel.exe and del.exe are in the resource section of the ransomware file. The dropped file selfdel.exe as shown in figure 2.0 will get the process name Samsam, and sleep for 3000 milliseconds, after which it will delete the Samsam ransomware process.

Figure 1.0 code of the selfdel.exe
The ransomware encrypts 328 file extensions.the list of file extensions are shown in figure 3.0 .Since the ransomware encrypts files with extension “.sql”, “.sqlite”, “.sqlite3”, “.sqlitedb” it will encrypt databases.

Figure 2.0 File extension targeted by Samsam ransomware.
The ransomware code makes the call to the API DriveInfo.GetDrives() to get a list of all the logical drives in the computer and will encrypt the files in these drives. The ransomware will encrypt the files in shared mapped SMB drives, CD drives, attached removable drives to the computer. Backups from the endpoint can often be configured to access the database via the mapped logical drive. In such configuration, database files which can be accessed via the logical drives will also get encrypted.

Figure 3.0 showing call to get the logical drives to the computer.
If the path of the directory contains “Windows”, “Reference Assemblies\\Microsoft”, “Recycle.Bin” the files in these folders will be skipped and will not be encrypted.

Figure 4.0 code showing ransomware skipping file in specific folders.
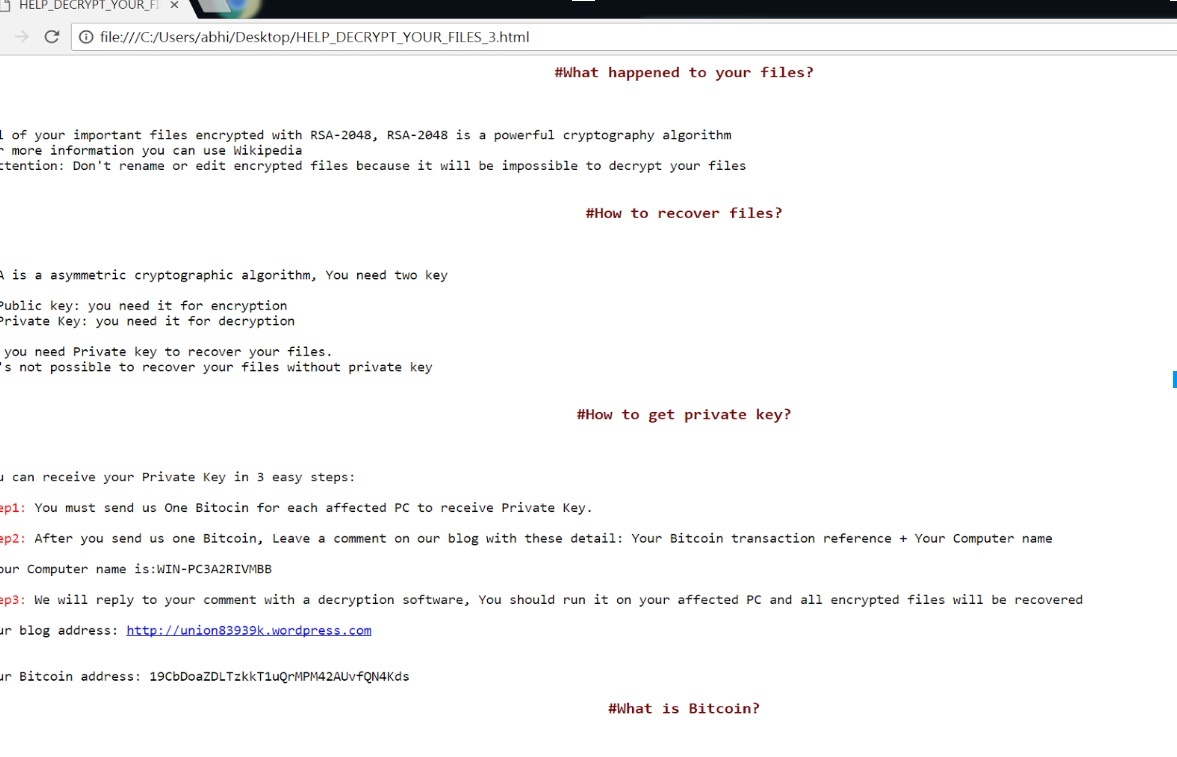
To create the encrypted file, ransomware creates a new file, writes encrypted data to it and deletes the original file. The new encrypted file will have file extension .encryptedRSA appended to the original file name. HTML file titled “HELP_DECRYPT_YOUR_FILES” having the ransomware note gets dropped to the directory.

Figure 5.0 showing ransomware note
Deception based detection:
Deception-based architecture involves distributing breadcrumbs and lures on endpoints. When these breadcrumbs and lures are accessed, alerts from the breadcrumbs and lures will be generated and get validated by the proprietary algorithm for ransomware infection. The version of Samsam used in the breach will get detected by ShadowPlex-R. Once the infected endpoint gets identified, it get isolated from the network to prevent the spread of infection.

Detection of Samsam in ShadowPlex-R
For further details about deception based architecture to prevent infection, I would encourage readers to read my blog Deception Centric Defense Against Ransomware. The blog details the advantages of deception based architecture over the traditional architecture to detect ransomware.
Conclusion:
Samsam ransomware gets activated by the threat actor after they have breached an organization, it becomes a challenge for the inline monitoring architecture to detect them. As discussed in the blog to execute samsam ransomware it requires the public key in a specific format from the command line argument. Detection architecture which relies on detonation in a virtualized environment to classify the file as malicious or benign, will not be able to provide public keys in the format which is required for samsam to execute and hence malware will not show its behavior when detonated in a virtualized environment. It will be a challenge for the detection architectures which relies on capturing the behavior in the virtualized environment to classify Samsam as malicious. Deception-based architecture detects and remediates during the execution of malware, hence it is a recommended architecture to prevent breaches and ransomware.
SHA256 of the analyzed file:
0f2c5c39494f15b7ee637ad5b6b5d00a3e2f407b4f27d140cd5a821ff08acfac
710a45e007502b8f42a27ee05dcd2fba
References:
[1] Allscripts recovering from ransomware attack that has kept key tools offline.