Resources
Tunneling for Network Deceptions
Patent Awarded to Acalvio Acalvio was awarded U.S. Patent No. 20,170,310,706, titled “Tunneling For Network Deceptions”. This patent forms the basis of the Deception Farms® architecture. This blog goes a little deep into the patent to talk about what the patented...
Deception and Compliance – It’s the Intent that Matters
Compliance is like an annual checkup at the dentist: Nothing good is likely to come of it and we want it to be as fast and painless as possible. In the first of two blogs on compliance, we’ll consider how best to think about compliance intent, and how deception can...
Ransomware Deja Vu: Louisiana Schools’ Emergency Alert
On 24 July, 2019 the State of Louisiana actually had to declare a state of emergency over what appears to have been a ransomware attack against at least three of the school districts within the state. So far, the districts impacted include Sabine, Ouachita, and...
Know Your Adversary, Before They ATT&CK
The Cyber Kill Chain If you’re reading this blog, you likely know the basics of the cyber kill chain. You might even be able to name a few of the seven stages in the kill chain, which lays out the steps adversaries take to attack and exploit their victims. Where you...
NIST’s Expertise on APTs: Gaining Serious Insight – Acalvio
If there's any organization that knows about dealing with advanced persistent threats (APTs) it's NIST. The US government is constantly targeted by the most sophisticated adversaries, and the attacks are directed at both the government agencies themselves, and...
“Amazon Firestick” is to “VCR”, as “Deception” is to _________
Complete the Analogy: “Amazon Firestick” is to “VCR”, as “Deception” is to _________. Correct Answer: “Honeypot” Remember your SAT or ACT exams with the analogy questions? If so you probably got this one right. For those of us old enough to remember, Video...
The Deceptively Simple Shortcut to Visibility
If you’ve ever had a security vendor pitch their wiz-bang internal network threat prevention solution, you’ve probably thought at some point “You’re getting ahead of yourself. First we need to know what’s going on, then we can talk about active controls on the...
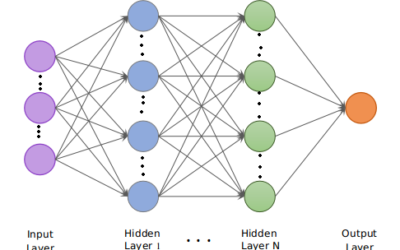
Using Deep Learning for Information Security – Part 2
Authors: Santosh Kosgi, Mohammad Waseem, Arunabha Choudhury, and Satnam Singh Deep Learning-based methods have been successfully applied to various computer vision and NLP based problems recently [1]. AI researchers have achieved statistically significant improvements...
Formjacking: Deception is your cure
Formjacking attacks embed JavaScript into ecommerce sites to siphon off credit card data.
Using Deception to effectively fight Ransomware
Deception could be a game changer in terms of detecting Ransomware.
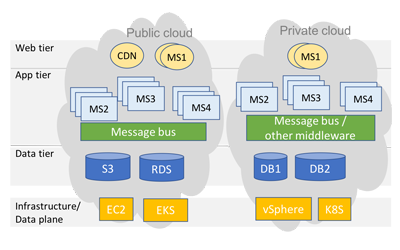
Advancing State of Art in Cloud Malware Detection
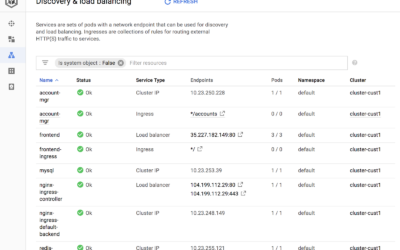
Detecting attackers with kubernetes driven deception in cloud-native applications
Deceiving Attackers in a Kubernetes World
Deceiving Attackers in a Kubernetes World