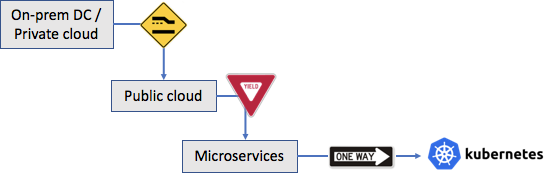
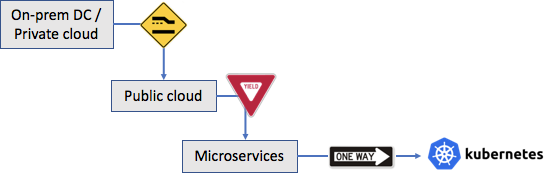
Enterprise workloads are rapidly migrating from on-prem data centers or private clouds towards public clouds, run by players such as Amazon and Microsoft. While CIOs and IT leaders have been spending the past few years reeling in these individual public cloud islands, it is increasingly becoming clear that enterprise infrastructure is going to be hybrid in nature and better to fully embrace the notion that enterprise infrastructure will span private clouds, and multiple public clouds. Considering each variant of the cloud has a different management, operational and security model, it is hard to achieve a common security posture that CIOs are comfortable with.
There is, however, some reprieve in the horizon, thanks to another orthogonal transformation well underway among developer communities, wherein developers are porting applications to a platform that is common across all clouds. Specifically we’re referring to the redesign of applications to use the microservice design pattern and being dockerized to run over the open-source Kubernetes platform. This porting over will allow enterprises to run application as-is in any Kubernetes cluster within private cloud (e.g., vanilla-K8S, OpenShift, PKS), or public cloud (e.g., EKS, AKS, GKE).
Why will having a common platform across clouds enable having a strong security posture? Two reasons. Firstly, in a common platform the nuances of underlying cloud are abstracted away and the capabilities, privileges, identities, tokens, accesses are all those configured in the Kubernetes layer, allowing for easier control, management and auditing. This also means that any security solution deployed to protect a Kubernetes workload is equally portable across clouds. Secondly, applications expose their dependencies in a common format (viz., Kubernetes/Helm descriptors and operators) allowing for easier posture assessment and enforcement. Being able to understand application behavior in a proactive manner allows for much more fine-tuned security measures.
While there will always be cloud-specific resources that the applications consume (e.g., AWS S3, GCP DataProc) causing heterogeneity that poses challenges to the posture, the convergence of the applications under a common runtime abstraction helps make tremendous headway into securing the applications. This is more so true from a malware detection point of view, as learned first hand by our efforts in exploring the place of deception technology in the Kubernetes based microservice workloads. More in a follow up blog. Stay tuned.